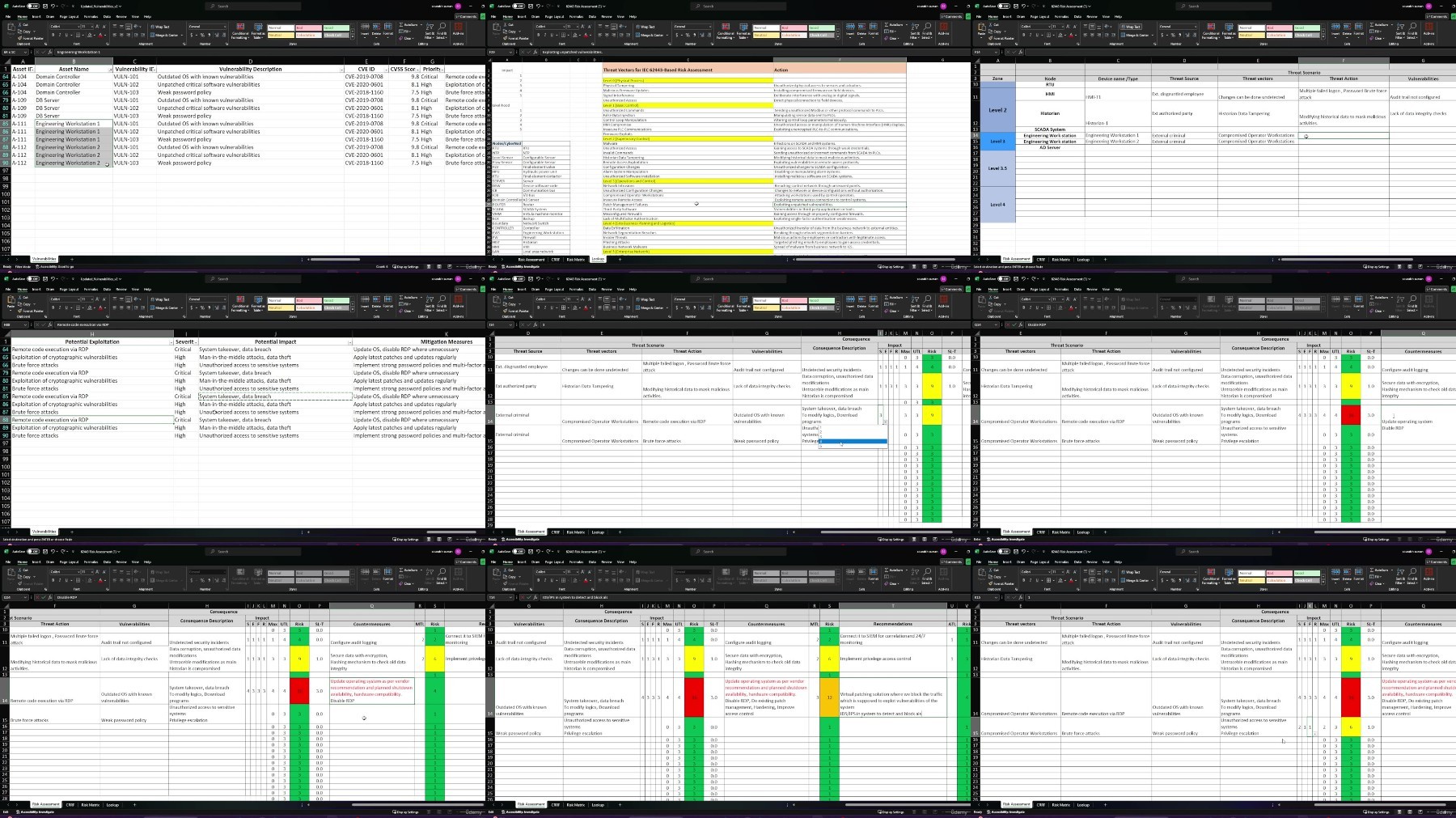
Practical 62443 Based Risk Assessment Exercise- Ot Security

Practical 62443 Based Risk Assessment Exercise- Ot Security
Published 8/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 2.56 GB | Duration: 2h 54m
Step-by-Step Guide to Conducting a 62443-Based Risk Assessment in Industrial Control Systems (ICS). Are You Ready ?
What you'll learn
Conduct Comprehensive Risk Assessments-Learners will be able to perform thorough risk assessments on Industrial Control Systems (ICS)
Develop and Implement Mitigation Strategies: Learners will learn how to develop effective mitigation strategies to address identified risks
Enhance Operational Security and Compliance: Learners will be equipped with the skills to enhance the overall security posture of their ICS environments
Create report and next steps after assessment
Requirements
Industrial knowledge of DCS/SCADA/PLC is mandatory, if you don't know don't buy!
No programming knowledge required, for core industrial professionals!
Understanding of ICS/OT environment
Prior experience required in ICS–-CAUTION, its mandatory!
Architecture awareness of OT systems
Description
Are You Ready to Master the Art of Cybersecurity Risk Assessment?In a world where industrial environments are under constant threat, understanding how to conduct a thorough, standards-based risk assessment is crucial. But let's face it—most courses out there leave you guessing, offering only a surface-level overview without the practical, step-by-step guidance you need. This course is different.Why This Course Is a Game-Changer:This is the course that finally demystifies the process of conducting a 62443-based cybersecurity risk assessment in a plant environment. We've taken the complex and often confusing world of ICS risk assessment and broken it down into a clear, actionable, step-by-step approach. By the end of this course, you won't just understand how to perform a risk assessment—you'll be able to do it with confidence.What You'll Learn:Step-by-Step Guidance: Every detail is covered. From understanding the foundational requirements of IEC 62443 to executing each phase of the risk assessment process, you'll follow a structured path designed for real-world application.Hands-On Experience: This isn't just theory. You'll dive into practical exercises, conducting risk assessments at different levels of an industrial control system. Learn by doing, and build the expertise that others only talk about.Comprehensive Coverage: Unlike other courses that skim the surface, this course goes deep. We'll walk you through everything from asset inventory and system architecture to identifying threats, calculating risk, and developing mitigation strategies.Why You Need This Course Right Now:Most courses leave you with more questions than answers, but this one gives you the full picture. If you're looking to gain a competitive edge and become an expert in 62443-based risk assessment, this is your opportunity. Don't settle for incomplete knowledge—this course is your roadmap to mastering the skills that are in high demand.Who Is This Course For?This course is perfect for cybersecurity professionals, ICS engineers, plant managers, and anyone who needs a clear, comprehensive understanding of how to protect industrial environments from cyber threats.Don't Wait—Secure Your Future in Cybersecurity Today!Enroll now and start your journey towards becoming a trusted expert in conducting 62443-based risk assessments. This is the detailed, step-by-step guide you've been waiting for—don't miss out!
Overview
Section 1: Introduction and Course Overview
Lecture 1 Introduction
Lecture 2 The importance of risk assessment in ICS environments.
Section 2: Virtual Tour and Understanding the ICS Environment
Lecture 3 Virtual Tour
Lecture 4 Asset inventory and classification
Lecture 5 System Architecture
Section 3: Terminologies used for Risk Assessment
Lecture 6 UTL, MTL & ATL
Lecture 7 Tolerable Risk , CRRF & SL-T Calculation
Lecture 8 Risk Matrix Explantion
Section 4: Practical Risk Assessment Workshop
Lecture 9 Materials
Lecture 10 Level 0 Risk Assessment
Lecture 11 Level 1 PLC Risk Assessment
Lecture 12 Level 1 Network Switch
Lecture 13 Level 1 NTP Server Risk Assessment
Lecture 14 Level 2 HMI Risk Assessment
Lecture 15 Level 2 Historian Risk assessment
Lecture 16 Level 3 EWS1&2 Risk Assessment
Lecture 17 Level 3.5 Firewall 2 Risk Assessment
Section 5: Reporting and Recommendations
Lecture 18 Creating the Risk Assessment Report
Lecture 19 Next Steps After the Risk Assessment
Control engineers, integrators, and architects who design or implement OT systems,System administrators, engineers, and other information technology (IT) professionals who administer, patch, or secure OT systems,Security consultants who perform security assessments and penetration testing of OT systems,Cybersecurity managers who are responsible for OT systems,Vendors that are developing products that will be deployed as part of an OT system
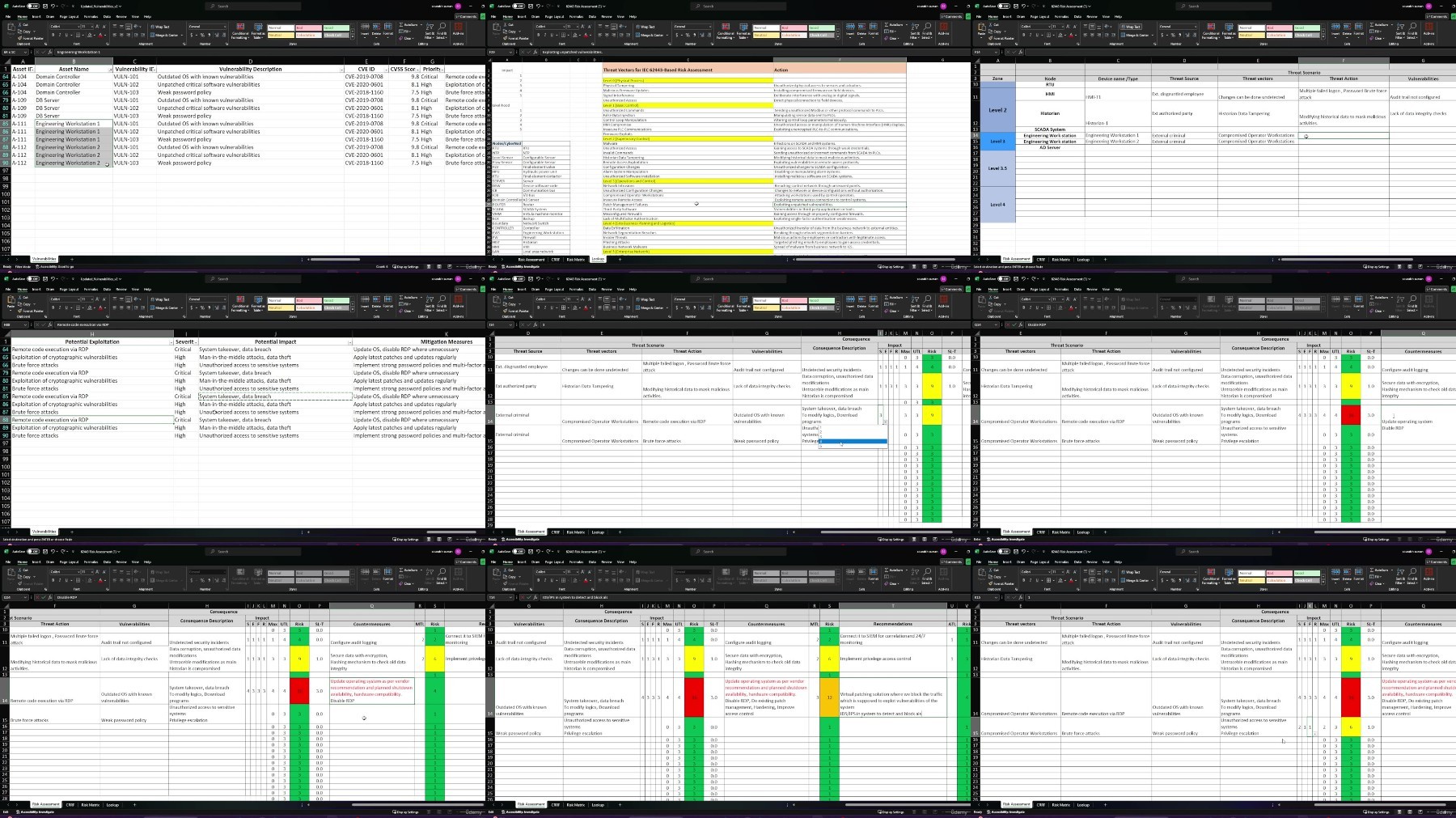
What you'll learn
Conduct Comprehensive Risk Assessments-Learners will be able to perform thorough risk assessments on Industrial Control Systems (ICS)
Develop and Implement Mitigation Strategies: Learners will learn how to develop effective mitigation strategies to address identified risks
Enhance Operational Security and Compliance: Learners will be equipped with the skills to enhance the overall security posture of their ICS environments
Create report and next steps after assessment
Requirements
Industrial knowledge of DCS/SCADA/PLC is mandatory, if you don't know don't buy!
No programming knowledge required, for core industrial professionals!
Understanding of ICS/OT environment
Prior experience required in ICS–-CAUTION, its mandatory!
Architecture awareness of OT systems
Description
Are You Ready to Master the Art of Cybersecurity Risk Assessment?In a world where industrial environments are under constant threat, understanding how to conduct a thorough, standards-based risk assessment is crucial. But let's face it—most courses out there leave you guessing, offering only a surface-level overview without the practical, step-by-step guidance you need. This course is different.Why This Course Is a Game-Changer:This is the course that finally demystifies the process of conducting a 62443-based cybersecurity risk assessment in a plant environment. We've taken the complex and often confusing world of ICS risk assessment and broken it down into a clear, actionable, step-by-step approach. By the end of this course, you won't just understand how to perform a risk assessment—you'll be able to do it with confidence.What You'll Learn:Step-by-Step Guidance: Every detail is covered. From understanding the foundational requirements of IEC 62443 to executing each phase of the risk assessment process, you'll follow a structured path designed for real-world application.Hands-On Experience: This isn't just theory. You'll dive into practical exercises, conducting risk assessments at different levels of an industrial control system. Learn by doing, and build the expertise that others only talk about.Comprehensive Coverage: Unlike other courses that skim the surface, this course goes deep. We'll walk you through everything from asset inventory and system architecture to identifying threats, calculating risk, and developing mitigation strategies.Why You Need This Course Right Now:Most courses leave you with more questions than answers, but this one gives you the full picture. If you're looking to gain a competitive edge and become an expert in 62443-based risk assessment, this is your opportunity. Don't settle for incomplete knowledge—this course is your roadmap to mastering the skills that are in high demand.Who Is This Course For?This course is perfect for cybersecurity professionals, ICS engineers, plant managers, and anyone who needs a clear, comprehensive understanding of how to protect industrial environments from cyber threats.Don't Wait—Secure Your Future in Cybersecurity Today!Enroll now and start your journey towards becoming a trusted expert in conducting 62443-based risk assessments. This is the detailed, step-by-step guide you've been waiting for—don't miss out!
Overview
Section 1: Introduction and Course Overview
Lecture 1 Introduction
Lecture 2 The importance of risk assessment in ICS environments.
Section 2: Virtual Tour and Understanding the ICS Environment
Lecture 3 Virtual Tour
Lecture 4 Asset inventory and classification
Lecture 5 System Architecture
Section 3: Terminologies used for Risk Assessment
Lecture 6 UTL, MTL & ATL
Lecture 7 Tolerable Risk , CRRF & SL-T Calculation
Lecture 8 Risk Matrix Explantion
Section 4: Practical Risk Assessment Workshop
Lecture 9 Materials
Lecture 10 Level 0 Risk Assessment
Lecture 11 Level 1 PLC Risk Assessment
Lecture 12 Level 1 Network Switch
Lecture 13 Level 1 NTP Server Risk Assessment
Lecture 14 Level 2 HMI Risk Assessment
Lecture 15 Level 2 Historian Risk assessment
Lecture 16 Level 3 EWS1&2 Risk Assessment
Lecture 17 Level 3.5 Firewall 2 Risk Assessment
Section 5: Reporting and Recommendations
Lecture 18 Creating the Risk Assessment Report
Lecture 19 Next Steps After the Risk Assessment
Control engineers, integrators, and architects who design or implement OT systems,System administrators, engineers, and other information technology (IT) professionals who administer, patch, or secure OT systems,Security consultants who perform security assessments and penetration testing of OT systems,Cybersecurity managers who are responsible for OT systems,Vendors that are developing products that will be deployed as part of an OT system